
Defcon 24 OpenCTF
A CTF solution by dr_dave contact me: dr_dave@hackedexistence.com
The Setup:
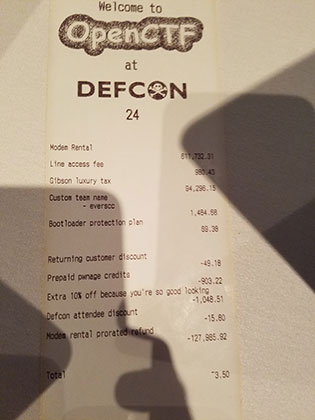
This challenge was a tough one – it required viewing the receipt that was provided to all teams that registered for the OpenCTF 2016 event at DefCon. Special thanks to pwnies for this collaboration ;-) (if you are the gentleman from pwnies that I collaborated with – please contact me – I forgot your name and want to give you credit!)
The Challenge - The Price is Right 100
You may want to double-check that receipt. I think the challenge organizers may have over-charged us! (it may be helpful to remember that all_f1@gs_l00k_liek_thiS) (the flag is NOT all_f1@gs_l00k_liek_thiS. that's just an example of what flags look like. And the approximate length of flags) (don't those prices look a bit weird? All of them?)
Solution:
This string is all of the numbers from the receipt put in a single string including the periods
611732.31980.4394296.151484.6869.3849.18903.221048.5115.80127985.923.50
Remove the periods and this is what you are left with:
611732319804394296151484686938491890322104851158012798592350
Fire up your python interpreter and do the following:
Python 2.7.12 (default, Jul 1 2016, 15:12:24) [GCC 5.4.0 20160609] on linux2 Type "help", "copyright", "credits" or "license" for more information. >>> a = 611732319804394296151484686938491890322104851158012798592350 >>> b = hex(a) >>> print b 0x61745f6c656173745f77655f6422646e745f676f5f3076655eL
This is the hex string – remove the hex header and decode it
>>> '61745f6c656173745f77655f6422646e745f676f5f3076655eL'.decode('hex')
Traceback (most recent call last):
File "", line 1, in
File "/usr/lib/python2.7/encodings/hex_codec.py", line 42, in hex_decode
output = binascii.a2b_hex(input)
TypeError: Odd-length string
Notice that python threw an error – trim off the last character in the hex string and try the decode again
>>> '61745f6c656173745f77655f6422646e745f676f5f3076655e'.decode('hex')
'at_least_we_d"dnt_go_0ve^'
We were able to submit that flag and have the scorebox accept it!
